Researchers have discovered a new malware in the MENA region called “Slingshot.” This malware attacks and infects its victims through compromised routers and can run in kernel mode, which would give more control over the victims device.
According to Kaspersky Lab’s report, the malware has been used for cyber espionage from at least 2012 until February 2018. Research’s are saying that many of the techniques used by this malware are unique and is incredibly effective at gathering information in a stealth manner, hiding itself from marked data traffic that can intercept without a trace from everyday communication.
The Slingshot operation was discovered after researchers found a suspicious keylogger program and created a behavioral detection signature to see if the code started appearing anywhere else. This signature triggered a detection that turned out to be an infected computer containing a suspicious file inside the system folder named scesrv.dll. Researchers are continuing to investigate the matter.
Per analysis of the file, it appeared to contain malicious code that was being executed. This library is loaded by ‘service.exe’ and is a process that has system privileges, the infected library was able to have the same level of privileges. Researchers discovered that a highly advanced intruder found its way into the very core of the computer.
In a Slingshot FAQ, researchers wrote:
This DLL then connects to a hardcoded IP and port (in every cases we saw it was the router’s IP address), downloads the other malicious components, and runs them.
To run its code in kernel mode in the most recent versions of operating systems that have Driver Signature Enforcement, Slingshot loads signed vulnerable drivers and runs its own code through their vulnerabilities.
Following infection, Slingshot would load a number of modules onto the victim device, including two huge and powerful ones: Cahnadr, the kernel-mode module, and GollumApp, a user-mode module. The two modules are connected and able to support each other in information gathering, persistence, and data exfiltration.
The most sophisticated module is GollumApp. This contains nearly 1,500 user-code functions and provides most of the above described routines for persistence, file system control, and C&C communications.
Canhadr, also known as NDriver, contains low-level routines for network, IO operations, and so on. Its kernel-mode program is able to execute malicious code without crashing the whole file system or causing Blue Screen—a remarkable achievement. Written in pure C language, Canhadr/Ndriver provides full access to the hard drive and operating memory despite device security restrictions, and [it] carries out integrity control of various system components to avoid debugging and security detection.
Kaspersky says that the most remarkable thing about Slingshot is its unusual attack vector. As investigation uncovered more victims, they found that many victims seemed to have been initially infected through hacked routers. The group behind Slingshot appears to compromise routers and place a malicious dynamic link library inside it that is in fact a downloader to download more malicious contents. When the router’s administrator logs into it, the router’s management software downloads and runs the malicious module on the computer.
At this time, it’s unknown how routers were hacked in the first place.
At this time, it appears that Slingshot’s main purpose seems to be cyberespionage. Analysis of the malware suggests it collects information like screenshots, keyboard data, network data, USB connections, passwords, clipboard data, and other desktop activity. But since the malware has kernel access, this basically means that it has access to virtually everything.
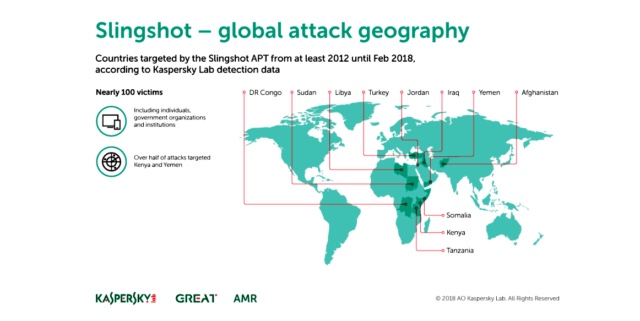
Researchers have found around 100 victims of Slingshot and its related modules, located in Kenya, Yemen, Afghanistan, Libya, Congo, Jordan, Turkey, Iraq, Sudan, Somalia and Tanzania. Most targets appear to be individuals rather than organizations, but there are also some government organizations and institutions involved.
“Slingshot is a sophisticated threat, employing a wide range of tools and techniques, including kernel mode modules that have to date only been seen in the most advanced predators. The functionality is very precious and profitable for the attackers, which could explain why it has been around for at least six years,” said Alexey Shulmin, Lead Malware Analyst, Kaspersky Lab.